In the digital age, it has never been more critical for organizations to safeguard personal data. As global awareness of the growing threat to privacy increases, governments are playing catch-up to ensure that those who handle personal data do so with adequate risk assessment systems in place.
A Privacy Impact Assessment (PIA) is effectively an early warning system when it comes to privacy. It is used to assess, identify and minimize the data protection risks of any electronic activity carried out by an organization which involves the personal information of data subjects.
For any organization which handles personal data, there are effectively two elements to the PIA process to be understood. Firstly, it is necessary to establish when the requirement for a PIA is triggered within your jurisdiction - and secondly, when required, how to undertake a PIA itself.
PIAs are becoming a central tool for demonstrating compliance with data protection obligations across European, US and Canadian privacy frameworks. Whilst there are many commonalities in PIA requirements under each regime, there are some key distinctions which are unique to each.
This article sets out some general guidance around the purpose and content of a PIA, before exploring the specific requirements of European GDPR, US and Canadian privacy regimes.
Summary
What is the purpose of a Privacy Impact Assessment and what should it contain?
Protecting the rights of individuals
The primary purpose of a PIA is to minimise the risk posed to the personal data held and processed by your organization - in other words, to protect the rights of individuals. A PIA will not necessarily eliminate 100% of the risks involved in handling personal data.
It is rather a mitigation exercise, allowing you to determine whether the risks posed can be adequately managed.
Protecting your organization
From a legal point of view, the secondary purpose of a PIA is to demonstrate compliance with national data protection requirements - in other words, to protect your organization.
Not only are PIAs a key element of meeting your accountability obligations, but using them appropriately is likely to protect your organization from costly enforcement action.
Commercial advantages
Setting aside the legal requirements governing the use of PIAs in any jurisdiction, there are a number of holistic benefits to having a robust PIA system in place:
-
Financial: Having a proactive PIA system should allow you to identify potential data protection risks early. This is likely to result in simpler, less expensive solutions to any privacy issues - as well as reducing project costs by minimising any unnecessary collection of data.
-
Reputation: Having a transparent and effective PIA system serves to reassure data subjects that your organization takes the handling of their personal information seriously. This cultivates a trustworthy reputation, and bolsters the confidence of the individuals concerned.
When is a Privacy Impact Assessment required?
The conditions which trigger a PIA differ slightly under GDPR-regulated, US and Canadian regimes. Each of these are explored in detail below. However, the following points are useful to bear in mind:
- General rule: In general, a PIA is likely to be required whenever an organization is carrying out an activity which may have an impact on the personal information of individuals.
- Jurisdiction: In Europe, both public and private bodies are subject to PIA regulations under the GDPR. In the US and Canada, they apply to public bodies only - not to private companies.
- Cross-border activities: Private organizations based in the US or Canada who handle data from inside European borders will nonetheless be required to comply with the GDPR.
- Ongoing obligation: Under all jurisdictions, the requirement to conduct a PIA where necessary is an ongoing obligation. It should be revisited whenever there is a change to the scope, purpose, or nature of your data processing activity.
What should a Privacy Impact Assessment contain?
Because each jurisdiction sets their own legislative requirements in respect of how a PIA should be conducted, it is important to refer to national guidance when carrying out an assessment.
However, broadly, the following elements are common to a PIA, regardless of where it is carried out:
- A detailed description of the processing activity that your organization plans to carry out;
- An assessment of the proportionality of this activity in relation to its intended purpose;
- An assessment of the risks posed to the rights of data subjects;
- How these risks will be mitigated; and
- Ongoing monitoring to ensure that the PIA remains up to date.
In order to get more specific, let's now dive deeper and take a look at the specific of a Privacy Impact Assessment according to the GDPR, US data privacy laws, and Canadian data privacy laws.
Privacy Impact Assessments under the GDPR
Legal framework
The requirement to conduct a PIA is created by Article 35 of the General Data Protection Regulation (GDPR). Member states have the freedom to implement this through domestic legislation.
Under Article 35(1) of the GDPR, both private and public organizations must undertake a DPIA in any situation in which they are processing information in a way which is likely to result in a high risk to the rights and freedoms of individuals. The Article 29 Working Party (WP29) has produced detailed guidelines to help organizations establish when a PIA is necessary. These are summarised below.
When is a Privacy Impact Assessment required under the GDPR?
Now, let's look at the various situations and use cases where a Privacy Impact Assessment is required or not under the GDPR.
Mandatory assessments: WP29 guidance provides three examples of situations in which a PIA will be mandated under the GDPR. These are:
- The use of systematic and extensive profiling or automated decision-making in order to make significant decisions about people.
- The large scale processing of “special category data” or criminal offence data.
- The large scale systematic monitoring of any publicly accessible place.
In the above circumstances, it is more or less certain that a PIA will need to be conducted, due to the high risk nature of the activities concerned.
Optional assessments: In order to determine when a PIA is necessary in all other situations, WP29 guidance sets out nine criteria which should be considered in order to assess the level of risk.
In most cases, the presence of a combination of any two of these criteria will indicate the need for a PIA. However, this is not a strict rule, and a PIA may still be needed when only one criteria is met.
If there is any doubt about whether an assessment is required, it is recommended that a PIA be carried out. Not only is this good practice, but it is also likely to protect your organization against any potential enforcement issues down the line.
The criteria to be considered are as follows:
1. Evaluation or scoring: For example, undertaking genetic tests in order to predict health risks.
2. Automated decision-making with legal or similar effect: Any processing in which the resulting decision may lead to discrimination against the individual concerned.
3. Systematic monitoring: Any processing designed to observe, monitor, or control subjects - particularly if done in a way which is impossible for a person to avoid (for example, monitoring carried out in a public area).
4. Sensitive data: For example, a hospital storing patient medical records, or storing information about a subject’s political ideologies or criminal convictions.
5. Data processed on a large scale: This is assessed by reference to the number of people affected, the volume of data, and the duration and geographical extent of the processing.
6. Matching or combining datasets: For example, two or more data processing operations being performed for different purposes or by different controllers.
7. Data concerning vulnerable data subjects: Processing the data of anybody who may not easily be able to consent - including children, employees, the mentally ill, and the elderly.
8. Innovative use or new technological or organizational solutions: New technologies (for example, the combined use of facial and fingerprint recognition for access control) can involve novel data uses which can pose a potentially high risk to the rights of data subjects.
9. Preventing data subjects from exercising a right or using a service or contract: For example, screening customers against a credit database for the purposes of a bank loan.
No assessment required: Your organization may determine that a PIA is not necessary in the following circumstances:
- Low risk: If, having considered the risk assessment criteria above, you determine that the data processing is not likely to result in a high risk to the rights and freedoms of data subjects.
- Pre-existing PIA: If you have already completed a PIA for another processing purpose which was very similar in nature, scope, and context.
- Legal basis: If your processing activity has a basis in, and is regulated by, EU or Member State law - as long as a PIA has already been carried out as part of that legal process.
- Optional list: Every member state is required to establish an “optional list” of processing activities which have been assessed as GDPR compliant and low risk. If your data processing falls within your country’s optional list, a PIA should not be required.
How to complete a Private Impact Assessment under the GDPR?
If it is determined that a PIA is required, the next step is to carry out the assessment.
Whilst GDPR requirements are designed to allow for flexibility and scaling depending on industry and organization size, every PIA must comply with the minimum criteria set out in Annex 2 of the WP29 guidance:
1. Description
- The nature, scope, context and purpose of the planned processing.
- The personal data involved, its recipients, and how long it will be stored.
- A functional description of the processing operation itself.
- The assets relied on (e.g. hardware, networks, people etc).
- How the processing will comply with approved codes of conduct.
2. Necessity and proportionality assessment
- What measures are envisaged to ensure proportionality and necessity of the processing (including specifying a legitimate purpose, ensuring lawfulness, and limiting data storage duration to what is necessary).
- What measures are envisaged to ensure the rights of data subjects (including protecting the rights of access, portability, and erasure, as well as international safeguards and providing adequate information to data subjects).
3. Management of risk
A description of the origins, nature, particularity and severity of the risks posed to data subjects (including the potential impact on individuals in the event of illegitimate access, or unwanted loss or modification of their data) and what measures are envisaged to mitigate these risks.
4. Consultation with relevant parties
- The advice of your organization’s Data Protection Officer must be sought.
- The views of the affected data subjects should be sought if appropriate.
5. Documentation, monitoring and publishing
You may be required to provide a copy of the PIA to your supervisory authority. It is not a requirement to publish the results of any PIA under the GDPR - however, doing so is good practice in the name of accountability and transparency.You should consult with your supervisory authority if the outcome of your PIA indicates that you may not be able to adequately mitigate the risks identified.
Privacy Impact Assessments under US data privacy laws
Legal framework
In the United States, the law governing PIAs is found under Section 208 of The E-Government Act 2002 (“the Act”). Unlike in Europe, US privacy law is set by individual states, and not by the federal United States government. Because of this, only government agencies are bound by the current framework.
It follows that private companies in the US are not obligated to undertake PIAs. However, doing so can be commercially valuable as a demonstration of protecting customer privacy. Any US company which does business in Europe will also be required to undertake a PIA in accordance with the GDPR.
The United States Department of Justice has published comprehensive guidance for government agencies on how to approach a PIA. The key elements of this guidance are summarised below.
When is a Privacy Impact Assessment required in the US?
Let's look at the various situations where a PIA is mandatory or not in the United States.
Mandatory assessments: Under the Act, a PIA should be carried out by government agencies in the following circumstances:
- New IT systems: Before developing or procuring any new IT systems which collect, store, or disseminate personally identifiable information about members of the public.
- New electronic collections: Before starting any new electronic collections which involve the personally identifiable information of ten or more members of the public.
- System changes: In general, a PIA will be also required at any time when a change to a system gives rise to a new privacy risk. Examples of situations where this might occur include:
- Conversions of paper records to electronic systems.
-
Adding new functions to a system which change previously anonymous personal data into a non-anonymous form.
-
Significant system management changes which create new potential avenues for exposure of personally identifiable information.
-
Merging of government databases (e.g. to create one central source of information).
-
New public access methods by which user-authenticating technologies (e.g passwords or biometrics) are applied to systems accessed by members of the public.
-
Adding of identifiable personal information to existing information systems from commercial or public sources.
-
New interagency uses by which agencies work together to use significant new uses or exchanges of identifiable information.
-
Changes to business processes which result in significant new uses of information.
-
Alteration in character of data, by which new information is added to a collection which raises the risk to the privacy of personal information.
No assessment required: Government agencies are not required to complete a PIA in the following circumstances:
- For any government run websites, IT systems or information collections which do not collect or store identifiable information about the general public.
- For any government run websites which allow their visitors to contact the site operator to provide feedback or request information.
- For national security systems which are exempt from the definition of information technology.
- If the requirements of a PIA have already been addressed in a “matching agreement” under the Privacy Act.
- If the requirements of a PIA have already been addressed in an “interagency agreement” for the merging of data for statistical purposes.
- If a system collects only non-identifiable information for a discrete purpose which does not involve matching with or retrieval from other databases which contain identifiable information.
- For minor changes made to a collection or system which do not give rise to new privacy risks.
How to complete a Privacy Impact Assessment in the US
There is some flexibility granted to government agencies under the Act in terms of the form that a PIA assessment takes. However, as a minimum standard, it should involve the following elements:
1. Content
- The information to be collected (e.g. nature and source).
- Why the information is being collected (e.g. to determine eligibility).
- The intended use of the information (e.g. to verify existing data).
- Who the information will be shared with (e.g. another agency).
- What opportunities individuals have to consent or refuse use of their information.
-
How the information will be secured (e.g. administrative and technological controls).
2. Analysis
The agency should then analyse the risks involved, and explain the decisions taken as a result of that analysis. The following considerations are relevant in approaching this task:
- Specificity: The depth of analysis should be appropriate to the nature, size and complexity of the IT system and information to be collected.
- IT development stage: For activities at this stage, privacy issues should be addressed specifically in relation to system development (including, for example, a statement of need, and analysis of functional requirements, alternatives, feasibility, cost/ benefit, and initial risk assessment). Because little may be known in the initial stages of development, this analysis may need to be updated as the project progresses.
- Major information systems: For major systems, an extensive analysis should be undertaken of the consequences of the planned collection and use of information, potential alternatives to this planned use, what measures are appropriate to mitigate the risks for each of these alternatives, and the rationale for the final decision made.
- Routine database systems: For simple databases containing only routine information, a standardised approach (for example, a checklist or template) can be used.
- Information life cycle: The information “life cycle” must be considered in all cases, including and information processing at each stage may affect individuals’ privacy (for example, collection, processing, storage, disclosure, and destruction).
3. Review and publication
-
Agencies must ensure that the PIA document is approved by a “reviewing official”.
-
Agencies must ensure that the PIA is made publicly available, unless publication would raise security concerns, or if it would reveal information relating to national security or the national interest.
Privacy Impact Assessments under Canadian data privacy laws
Legal framework
In Canada, the requirement to undertake a PIA is a policy requirement created by the TBS Directive on Privacy Impact Assessment (the Directive). As is the case in the US, privacy law is handled at a provincial, rather than federal level in Canada.
It is, therefore, currently only federal public sector institutions who are required to comply. Although this means that private companies are not obligated to conduct PIAs, any Canadian organisations which handle data in or from Europe will nonetheless be required to comply with the GDPR.
The Office of the Privacy Commissioner of Canada (OPC) has published guidance setting out PIA requirements for public sector institutions, the key elements of which are summarised below.
When is a Privacy Impact Assessment required in Canada?
Let's consider the instances where a PIA is mandatory, optional or not required in Canada.
Mandatory assessments: Before considering whether or not a PIA is required, the OPC is clear that the institution concerned must ensure that it has legal authority for the activity that it proposes to undertake. Thereafter, a PIA will generally be required in the following circumstances:
- When personal information may be used in a decision-making process which has a direct impact on the individual concerned (otherwise known as an administrative purpose). This may include, for example, making an immigration decision, or undertaking a criminal investigation.
- When an existing activity undergoes a major change in which personal information will be used for an administrative purpose for the first time.
- When an existing activity undergoes a major change as a result of transferring or outsourcing to another government department, or to the private sector.
Optional assessments: Even if no decisions are made about individuals, institutions are still encouraged to undertake a PIA if there are any potential privacy risks involved in their planned activity. Each project should be considered on a case by case basis, taking into consideration the following risk factors:
- The amount of personal information involved;
- The level of sensitivity of that personal information;
- The level of sensitivity in the arena in which the activity is planned;
- The number of people affected;
- Whether those people are a vulnerable portion of the population;
- The likely impact on these individuals;
- The duration of the activity; and
- Whether the activity involves any of these additional risk factors:
- The use of personal information for secondary purposes;
- The sharing of personal information outside of the institution;
- Any profiling or predictions of behaviour;
- Any automated decision-making;
- Any systematic monitoring of people;
- The collection of personal information without notice or consent; or
- Any data matching (i.e. linking of otherwise unrelated personal information).
How to complete a Privacy Impact Assessment in Canada
The initial process of determining whether a PIA is required doubles up as a preliminary risk assessment. The outcome of that process will determine the level of analysis which is likely to be required as part of the PIA.
If the activity is simple and low risk, a simple, brief report may be sufficient to meet the requirements of the PIA. If the activity is high risk, the PIA will need to be more in depth.
1. Planning
At an early stage, institutions should formulate a plan and establish the scope of the PIA to be undertaken.
This process should include describing the planned activity, establishing which personnel or departments need to be involved, and consulting with relevant stakeholders.
2. Necessity and proportionality
If the planned activity has been identified as high-risk, it is necessary to undertake an in-depth examination into whether it is necessary, and whether it can be done in a proportional way. The following steps should be completed:
- Consider the impacts on the right to privacy at the earliest possible stage;
- Evaluate the necessity, effectiveness, proportionality and intrusiveness of the activity;
- Document the rationale for proceeding, using evidence to support the decision;
- Ensure that the planned activity is necessary, effective, proportional and minimally intrusive before proceeding further.
3. Risk analysis
OPC guidance provides a suggested framework for the risk analysis section of the PIA. As a minimum, institutions should identify each risk posed to personal information, along with the likelihood of that event occurring and the extent of the impact on individuals which would result if the risk occurred.
The OPC recommends that the proposed activity is assessed against the following principles. The examples listed are not exhaustive, and institutions should refer to the full guidance where required:
- Accountability: Staff may not be adequately trained to protect and flag privacy concerns, and data subjects may not know who to contact with privacy queries.
- Limiting collection: Personal information could be collected without a clear purpose, or when it is not strictly necessary for the activity being undertaken.
- Direct collection: Individuals may not be aware that their data has been collected. They will have no way to correct inaccurate data if they are unaware of the collection.
- Retention: Personal information may be stored for longer than necessary, or may not be stored for long enough to allow individuals to obtain access to it.
- Accuracy: Personal information stored could be inaccurate, and an institution may make decisions based on inaccurate data.
- Disposal: Personal information may not be disposed of properly, and may end up being accessed without authorisation as a result.
- Limiting use: Personal information provided for one purpose may be used for a secondary purpose without the consent or knowledge of the individual concerned.
- Limiting disclosure: Personal information could be shared with third parties without the consent or knowledge of the individual concerned.
- Safeguards: Security breaches could lead to unauthorised access to personal information, and the institution may not have the means to detect this or respond.
- Openness: Notices informing individuals about the collection and use of their personal information may not be easily visible to them (e.g. buried in the small print).
- Individual access: Inadequacies in systems in place to deal with access, correction or disposal requests could lead to difficulties and delays for individuals.
4. Mitigation measures
Once the relevant privacy risks have been identified, mitigation measures should be identified.
The objective is to minimise risks as much as possible before assessing whether any residual risk is at an acceptable level. Some suggested mitigation measures include:
- Accountability: Identify who in the institution is responsible for privacy issues, train staff, and develop policies and procedures for privacy and handling public queries.
- Limiting collection: Have a clear purpose for data collection, collect only what is needed, and dispose of information appropriately in the event of over-collection.
- Direct collection: Collect information only from reliable sources, notifying individuals at the time of collection. Have a process for dealing with requests to correct data.
- Retention: Establish both minimum and maximum retention periods. Conduct regular audits to ensure that these periods are being kept to.
- Accuracy: Regularly test the accuracy of information gathered, and ensure that there is a system in place to allow individuals to have inaccurate information amended.
- Disposal: Ensure robust systems for the disposal of personal information, or configure systems to automatically delete data at the end of the retention period.
- Limiting use: Inform individuals of the precise planned use for their personal information, and have a process for seeking consent for secondary use if necessary.
- Limiting disclosure: Inform individuals of any third party disclosures, and have robust security agreements with any third parties with whom data is shared with consent.
- Safeguards: Implement a variety of physical, technical and digital safeguards to protect personal information, and implement a breach response procedure.
- Openness: Provide publicly available information about your personal information handling practices in an accessible way, and in a variety of formats.
- Individual access: Develop a clear process for responding to access and correction requests, and for informing third parties if inaccurate information has been shared.
5. Approval, reporting and monitoring
Before a PIA can be published, it must be subject to internal approvals from an institution’s relevant officials. It is their job to ensure that the final PIA has met all of the requirements under the law. Institutions are then required to publish certain sections of its contents (the details of which are set out in the Directive).
There should be an ongoing assessment of whether the measures implemented are effectively mitigating risk, as well as monitoring and re-assessing when there are significant changes to the privacy environment.
Navigating international regulations with Didomi
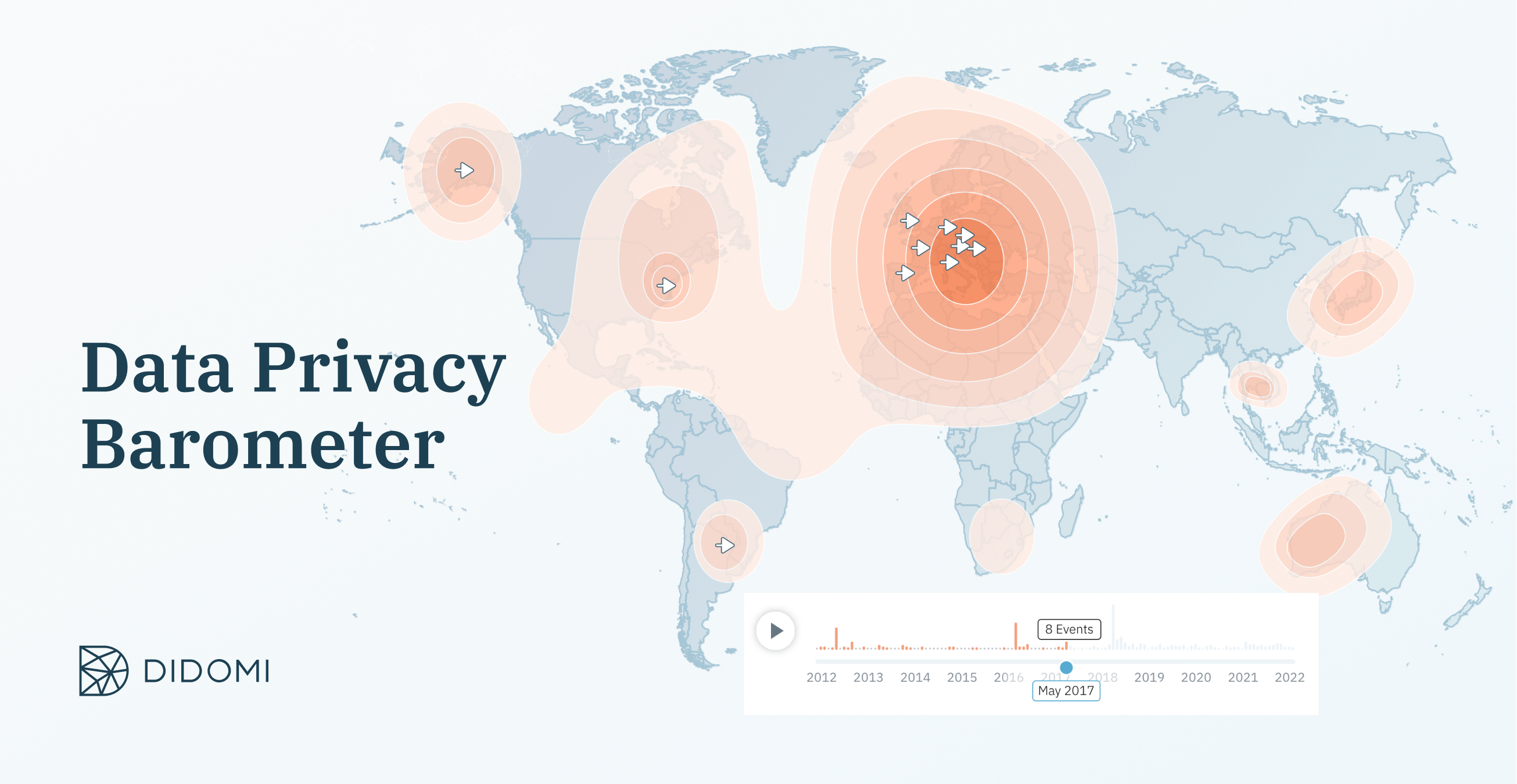
As we can see with the example of Privacy Impact Assessments, ensuring your organization is compliant all around the world is a difficult task and can become overwhelming. Through consent and preference management solutions, as well as free tools such as the Data Privacy Barometer, Didomi assists thousands of businesses in navigating compliance and regulations around the world.
To learn how we can help with your specific privacy needs, schedule a call with one of our experts:







